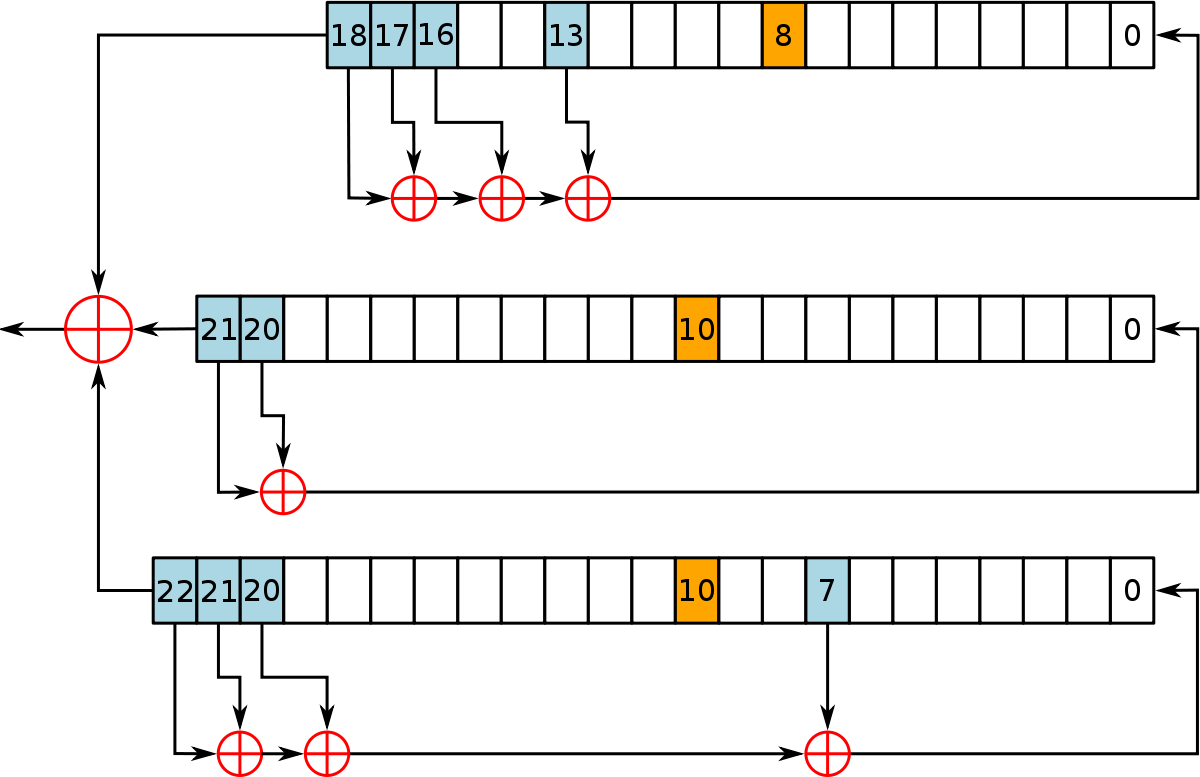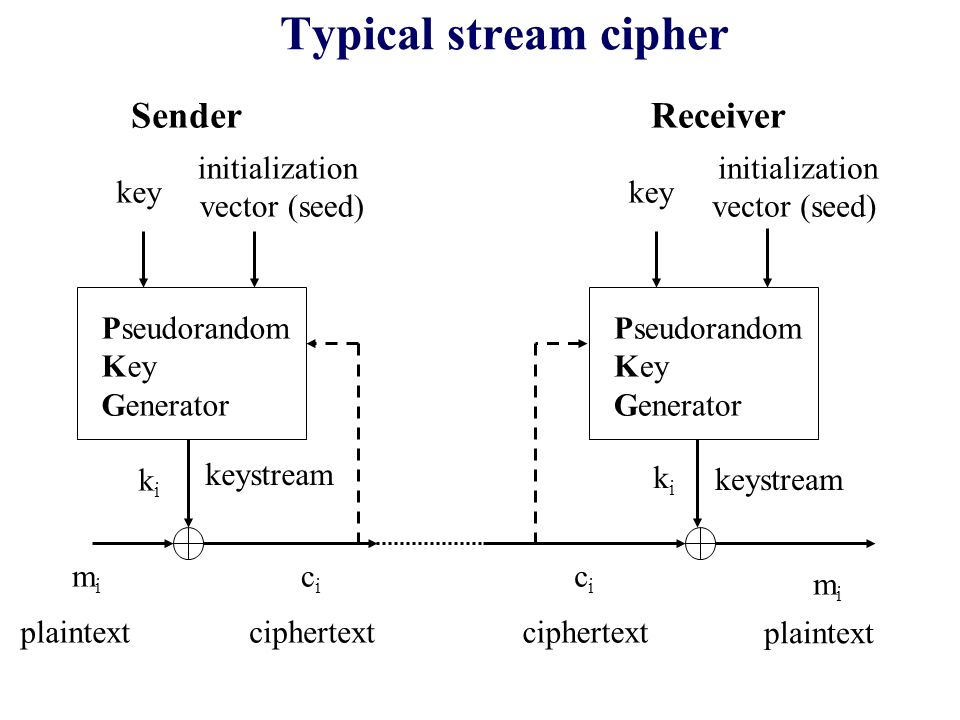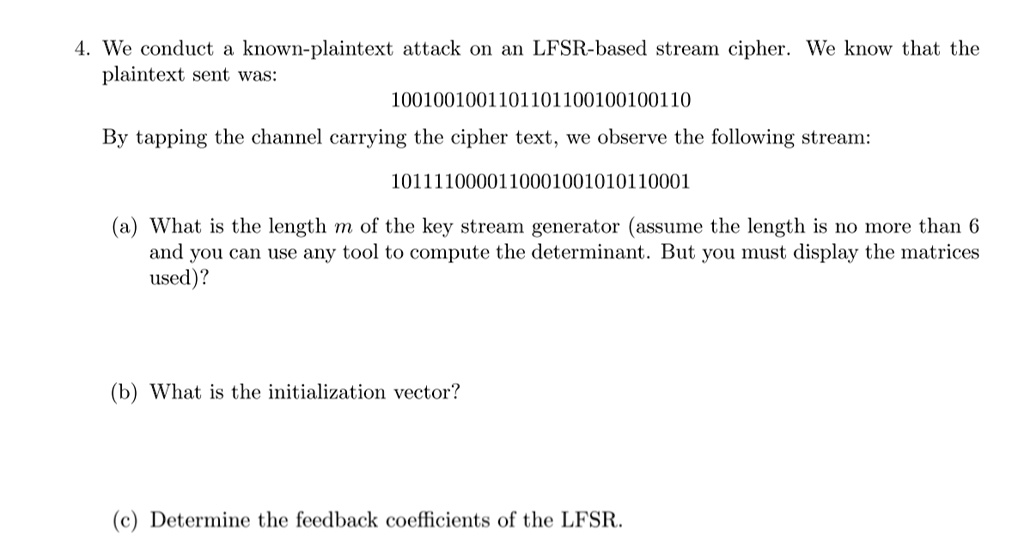
SOLVED: We conduct a known-plaintext attack on an LFSR-based stream cipher. We know that the plaintext sent was: 1001001001101101100100100110. By tapping the channel carrying the ciphertext, we observe the following stream: 1011110000110001001010110001.

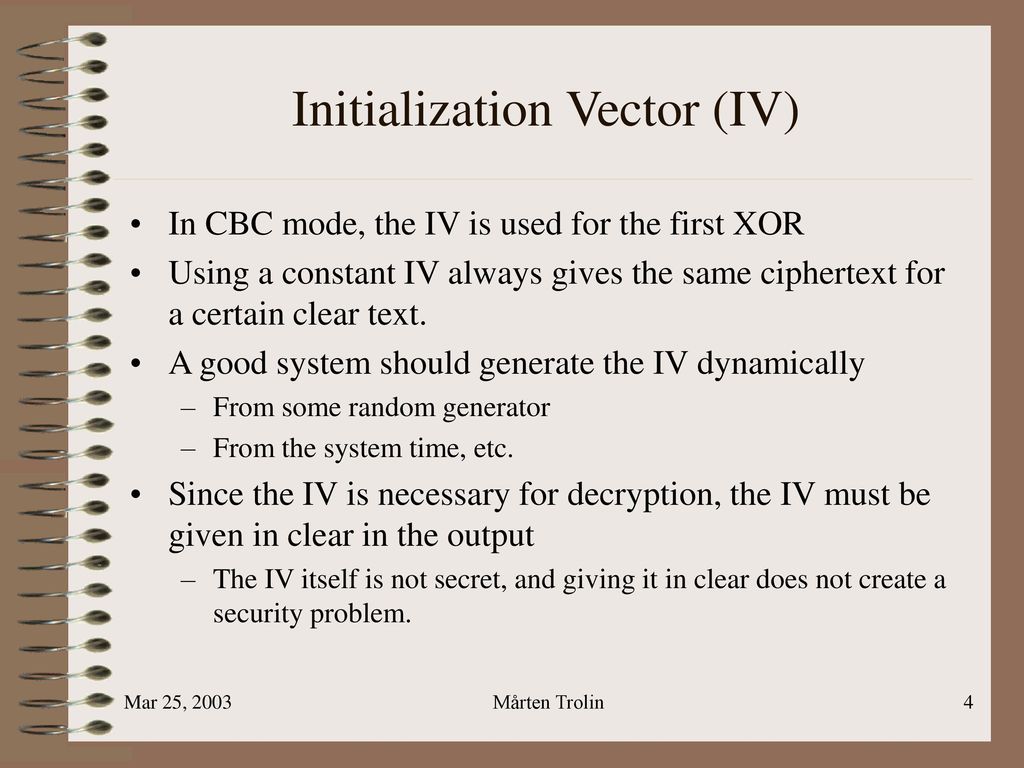
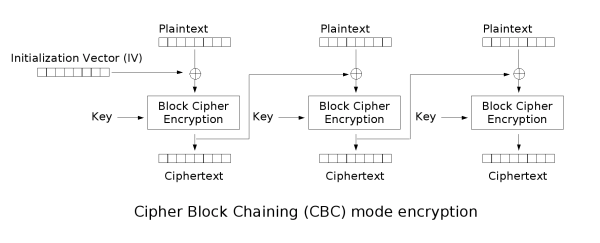
Cryptopals: Exploiting CBC Padding Oracles | NCC Group Research Blog | Making the world safer and more secure

encryption - When using AES and CBC, is it necessary to keep the IV secret? - Information Security Stack Exchange